Samizdat Strategies 3 - The What
There are ways around the Tech Lords' censorship, if you seek them out.
-
Tools:
Freedom-loving Americans are slowly coming to grips with the inescapably grim fact that we no longer live in a freedom-loving America. It's more accurate to say that we live in a land ruled by elites who hate ordinary rubes having any freedom at all, especially where we dissent from what the elites want us to think or do.
Nevertheless, all is not lost, and there are still actions us little guys down on the ground can do to protect ourselves and preserve the possibility of a restoration of American principles. In the first article in this series, we explained why it is now a matter of pressing urgency to make it more difficult for the enemies of free speech, individual freedom, the right to be let alone, freedom of conscience, and other ideas we hold dear to find out just how strongly you, personally, disagree with them.
The Gray Mirror pointed out that Harvard, Yale, the New York Times and the Washington Post are all on the same far-left socialistic tyrannical page in 2021. They were on the same page in 1951, but there's a crucial difference - they used to favor vigorous discussions of ideas, even ones they disagreed with.
They were confident enough in the superiority of their ideas that it wouldn't have occurred to them to block anyone from spreading opposing ideas or to try to destroy people who disagreed. Now they not only feel that the "cancel culture" is OK, they're convinced that they have a duty to destroy anyone who disagrees.
That's why the most important step to protect yourself as a non-celebrity nobody is to make it hard for them to find out what you really believe.
Search Engines
The Federalist explains how Google manipulates search results to hide things they don't want you to see and we've discussed the private information about you which Google records and sells. Step 1 is obvious: stop using Google for searches that might in any way be suggestive or compromising. Everybody in the country wears jeans and uses toilet paper, so there's no harm in using Google to search for those if you can still find them - but news? Never!
Instead, consider using https://duckduckgo.com which doesn't track you or store what you search or click on. To be honest, that search engine isn't as good as Google, but it will improve with time and increased usage. It does, however, find one of our articles which Google won't. Our site has a search engine text box at the upper right. If you search for let a thousand flowers wilt, google won't find it even though they claim to have indexed our site. You can use google.com to search, and you won't find it even if you tell Google to focus on our site. If you ask duckduckgo for let a thousand flowers wilt site:scragged.com, it finds it.
The fact that DuckDuckGo ranks pages by relevance instead of by political correctness is ample justification for using them, even aside from the privacy implications. You probably don't want to abandon Google abruptly, but you should immediately shift political searches elsewhere. Your browser has a setting which lets you choose a default search engine; tell it to use DuckDuckGo.com.
As we saw earlier, for the same reasons it's risky to use Gmail, Yahoo mail, Microsoft mail, or Facebook messaging because their algorithms read it all and retain all your data. Instead, the https://mail.protonmail.com/login mail service is based in Switzerland, outside the jurisdiction of US courts. Proton keeps copies, but encrypts all your mail so that even they can't read it without knowing your password - which, the Supreme Court has ruled, is covered under your Fifth Amendment protections. The free tier has limited mail storage, but you shouldn't be storing your email in the web anyway.
Be warned: sending from Proton to any other mail system defeats the purpose of encryption. Other mailers can't read encrypted mail so Proton sends it in the clear. Email addresses must always be sent in the clear or the mail won't go through; that's how every intelligence service in the world learned about the illegal mail server at clintonemail.com.
Observers will not only see your entire Proton conversations with other mail networks, they'll find out that you have a Proton account which will make them suspicious. The best practice is to use Proton exclusively for Proton-to-Proton communications where they don't have to transmit your address in a form other mailers can read, and leave it at that.
You also have to be aware that this protects you from casual search by civilians, but as "Don't Trust Those 'Secure' Messaging Apps" points out, "the American intelligence community has a heavily documented record of planting backdoors in software." Ken Thompson, the creator of UNIX, warned us, "You can't trust code that you did not totally create yourself." If you attract the active attention of Leviathan, nothing can save you - but systems like Proton can make that unhappy event less likely.
Email Clients
Using web mail saves you disk space because your messages live in the cloud, but there's a problem - if your provider decides to deplatform you, you won't be able to access your stored mail or your contact list. At a minimum, it would be a very good idea to periodically generate a backup of your contacts. Gmail and Linked In both let you do that.
Don't think that having your contact list on your phone will save you - when Google and Apple decided to deplatform Parler, the Parler app disappeared from all the smartphones that had downloaded it, just as books disappeared from Kindle when Amazon decided it shouldn't have sold them. Use Gmail's feature to download your contacts into a text file you can save on your personal computer safely at home, or if you're really concerned, someone else's.
The free Thunderbird mail client at https://www.thunderbird.net/ can sync with Google's contact list and also lets you save the list on your hard drive. This reduces the damage that would be done if you aroused enough anger to be cut off from your mail.
Its usual configuration has another virtue: it downloads copies of all your email to your local computer system. This can take up a great deal of space, but means that if the Tech Lords throw you off their servers, your message history will be preserved where they can't easily get to it.
A word of caution: Thunderbird is offered by the Mozilla foundation, which has come out publicly on the side of doing even more to drive non-elite thought off the public Internet. You may want to configure Thunderbird not to update itself automatically, just in case they decide to send you a version that will wipe out your data. This isn't terribly likely, since it's open-source and anyone who wants to can look into the code (and many do), but you never know, and certainly not the instant a new version is released.
Standard email clients, such as Thunderbird, use two different protocols for email handling. The newer and more common one called IMAP, leaves your email in the cloud on your email server but downloads a copy to your local system. This is convenient because you can have multiple different devices all using your same email account, such as your desktop PC and also your smartphone.
The older POP/SMTP protocol option is still supported by all major email clients and servers, but it has a twist: when it's used to download a message, that message is deleted from the remote server. Now it exists only on the computer that downloaded it, and nowhere else readily accessible.
This isn't super convenient for modern life. But, if your mail isn't stored in the cloud, it's harder for anyone to use algorithms to look over your email as part of a global scan looking for undesirable deplorables. Sure, there may be any number of caches and backups kicking around across the Internet where your mail is still around, but unless someone powerful is digging into you specifically, they won't likely come to light.
The American Thinker article we cited in part 2 explained the need for an "agnostic browser." The Federalist article cited above explains:
Use Brave for your browser on all your screens (phones, tablets, laptops, desktops, etc.).
Brave will not only get you away from Google's Chrome browser that your phone uses if you have an Android (Google) system, it will also get you using the search engine DuckDuckGo instead of Google.
The Federalist article cited just after the heading Search Engines, gives more information about Brave and explains how to download and install it.
The Right to Comment
As an alternative to Brave, the Dissenter browser lets you preserve your right to mock the powerful by posting comments everywhere. In its early days, the great advertised virtue of the World Wide Web was that it meant everybody could talk to everybody.
It didn't take long for powerful folks to realize that they don't want everybody talking to everybody, at least not privately and freely, because much of what we peasants say reflects poorly on them.
Many web sites have disabled comments either because site owners didn't appreciate negative comments from dissenters or because the Tech Lords threatened to blackball the sites if they kept accepting comments the Tech Lords didn't appreciate. A customized browser, Dissenter, allows you to fulfill your desire to comment on sites where comments are not allowed.
Read "Dissenter Review 2020 - The Ad Blocking 'Free Speech' Browser by Gab" which describes two Dissenter-related controversies raging in the nerdier corners of the Internet.
One comes from its origin. The other comes out of the censorship war raging across the Internet.
The article then explains the Dissenter comment feature which started out as a browser extension. It let you put a comment anywhere on the web, but it is visible only to someone who also viewed the site through a browser which had the Dissenter extension. This high-tech samidzat is visible only to those who are in the know.
Letting peasants criticize thin-skinned snowflakes led both Firefox and Chrome to ban the Dissenter extension, so Gab offered the Dissenter browser. The Dissenter extension was popular enough to infuriate the Tech Lords and help you find like-minded people, but it remains to be seen how many people will want to dissent from web sites badly enough to switch browsers.
The article has many more dramatic details of the ongoing censorship wars. Dissenter is based on Brave, so it has all the Brave privacy features plus the ability to spread graffiti across the World Wide Web.
Sneaking Around in the Dark with TOR
There is another browser with even more powerful privacy measures: TOR.
When you want to browse a website, we all know how to do that: enter gop.com into the URL field of your browser, and up pops the Republican Party website, at least for now.
The trouble is, your browser sent the request for gop.com out to your local ISP which then bounced its way across the Internet until it finally found the right server. Everyone in between knows someone was looking for the Republican Party, and, since your request contains your IP address to help the reply get back to you, it can be traced to you from any point along its path.
It doesn't matter if the site itself is secure and displays that little lock: other observers may not be able to see what you and the GOP said to each other, but they can know that you reached out to them. In the world we now live in, that may not be something you want known.
That's where TOR comes in: It uses its own anonymized routing system and fast-erasing nodes around the world to ensure that there's no way any snoops can discern who is asking for what. Your request might go to a primary server in Denver; be re-addressed and sent to Poland; re-addressed again and routed to Japan; then, with yet another address, finally make its way to wherever the Republican Party servers are. Their response makes its way back through the same route. As soon as you stop browsing, all the routing records in between are wiped from the intervening servers.
Now, as with most of the techniques we're discussing, if you have gotten the attention of Joe Biden's inquisitors, TOR will provide no protection whatsoever because they'll force your ISP to record all your traffic for them. It does, however, make it very difficult for even the government to discern your browsing history after the fact. Your run-of-the-mill BLM doxxer will have an even harder time and likely move on to an easier target.
There is one caveat - you can't use TOR to access web sites where you have to log on by providing credentials. The whole point is that nobody knows who's looking at the web site, not even that site itself. This doesn't work all that well for establishing your identity to a shopping site.
If this setup sounds shady and complex... you're not wrong. TOR is used by a fair number of nefarious sorts for all sorts of things we want nothing to do with. For this reason, some networks block TOR traffic entirely, and in certain circumstances mere usage of TOR can attract attention. You definitely shouldn't try it on your corporate network, for example.
But similar protocols are used by many computer games, so TOR traffic is less suspicious if it originates from a residential Internet connection. The TOR browser by default does not allow tracking cookies from the search engines, so even if you use Google in TOR, it won't be able to discover that you're a Republican, or even who you really are unless you log in to Google which defeats the whole point of using TOR.
All that anonymizing and world-girdling makes TOR slow so you'll use Dissenter or Brave for most browsing.
Don't be Microshafted
As far as we're aware, although Microsoft is a ruthless business competitor and its employees donate exponentially more money to Democrats than to Republicans, the firm hasn't deplatformed anyone for political reasons. Amazon famously threw the Parler web site out of its cloud and both Google and Apple deleted the Parler smartphone app from many phones, but we've never heard of Microsoft doing anything similar.
So Microsoft might not decide to damage you for political reasons. Nevertheless, you might want to avoid the Microsoft tax.
That's going to get worse. Microsoft can't improve Office enough to persuade people to pay for upgrades, so they're trying to force you to edit and store documents in their cloud. They hope the subscription model will replace some of the revenue they've lost because people see no reason to upgrade.
But doing this make you subject to whatever unforeseeable future changes might occur in Microsoft's corporate structure. It's practically a given that any changes in their mahogany row will push the entire corporation ever further to the left. Eventually, it'll be standing foursquare for fascism like the rest.
If you must communicate with people in businesses which use MS Office, you'll more or less have to stick with Microsoft to be able to send clients documents they can read. There are free Office substitutes, but Microsoft is adept at making subtle changes to its data format so that rival programs can't display documents produced by competing products in quite the way they were intended.
Fortunately, Microsoft Office has been around for a lifetime, in a gazillion versions going all the way back to MS-DOS floppy disks, and Microsoft has been historically quite careful about reverse-compatibility. Cloud-only Office versions are a relatively new development; Microsoft Office 2010 can be installed and run entirely independently, and is perfectly well able to read the most modern version of documents.
There are so many hundreds of millions of copies kicking around that this is likely to remain so for a long time to come. It's even possible to buy a perfectly legal license code on the aftermarket - for all Microsoft's legendary sharp business practices, it didn't occur to them to write their licenses as being non-transferable until recently. So there's an entire cottage industry of finding antique computers headed for the landfill that had a legal copy of Office installed on them, extracting the code, and selling it on.
Operating Systems
Installing Linux used to be a decent way to earn geekiness bragging rights, but it's gotten a lot simpler over the past two decades. Opensource.com has an introduction to Linux, the most common non-Windows desktop and laptop operating system in the world. Searching for "open source Linux versions" finds many. Each version has fervent supporters, so start with a version with many users who can help you:
Popular distributions include Elementary OS, Fedora, Mint, and Ubuntu, but there are others. It's a common saying that the best Linux distro is the one that works best on your computer, so try a few to see which one best suits your hardware and your style of working. [emphasis added]
Their saying "try a few" is a tribute to the fact that these programs are free and it doesn't take long to install one. You can cycle through many versions to find the fairest of them all for you.
Ask duckduckgo.com for
The search generally gives you an URL for the website of the group that maintains the version. Most such web sites have an About page that explains why their particular variant is unquestionably the best of the bunch.
Ubuntu is said to be the easiest to install and manage - you won't even need a root password - but some of our colleagues tell us it's bulking up and won't run well on older, less potent hardware. Mint's web page says they built on Debian and Ubuntu and that Mint requires very little maintenance. If you just want to install one and don't care how well it fits your needs in detail, just go with Ubuntu for the large fan base and ease of install. If you decide to look into the differences between distributions, you'll have to read the descriptions and perhaps participate in the discussion groups to see which one best appeals to you.
Hanging Eleven
If you want to take a stroll on the wild side, search for "tails linux usb." Tails is a Linux distribution which runs from a USB stick instead of actually being installed on the PC. This is intended for private, secure usage of random public computers such as the ones which will be freely available in your local library if Democrat tyrants ever allow them to reopen.
It uses the Windows mouse, keyboard, and network interface to run its code directly from the USB stick; the data never touch the hard drive. It uses the Tor browser so that nobody will know which public library computer you used. If you download anything, it's encrypted and written on the USB, leaving no trace on the computer itself.
The "About" page tells how it works. Even if you aren't interested in installing it, you'd find it to be an interesting read.
As with everything else, if the Gestapo is after you specifically, this won't help much: the Men in Black will simply install a keylogger on every computer in the libraries near you. Short of that, Tails is as close to securely private as it's possible to get.
Office Replacements
There are open source Office competitors. Open Office has been downloaded 300 million times. It is written in Java to run anywhere. Libra Office runs on Linux, MacOS, and Windows.
You could also use Google Docs - but if you want to do that, you clearly haven't been paying much attention to this series! Not only does that put all your information in the cloud where the algorithms can get at it, it does so on the cloud owned by the biggest and baddest searcher out there.
So Where Do We Go From Here?
This article has covered a number of geek-friendly ways to get information, that can work quite well... if you're willing to make a pretty serious investment in geekiness. That's the situation for people living under the thumb of the Chinese Communist Party. Geeks have always been able to tunnel through the Great Firewall of China and research forbidden topics such as the Tiananmen Square massacre.
The problem for an informed geek, then, is - now what? If you try to share the information with non-geeks, that is, anyone with a normal email account, the government will quickly find out that you're a spreader of intellectual contagion and shut you down.
That's why we don't recommend using an encrypted email system such as Proton except to communicate with others who have one. Keeping one-on-one channels hidden may help you find and spread information, but to a very narrow group.
Surely we're not so far down the road of totalitarianism that the only hope for conservatism is to hide in a hole and pull it in after us? Perhaps not. In the next article in this series we'll explore more conservative-friendly channels that are, or at least could be, in wider use. Switching to them will take audience, and thus money and stock price, from the Tech Lords.
"But," we can hear you say, "they only make a few bucks from little 'ol me." That may be true, but you can sink a battleship if you put enough gravel in it, one rock at a time. So let's throw rocks at them - metaphorically speaking of course!
-
Tools:
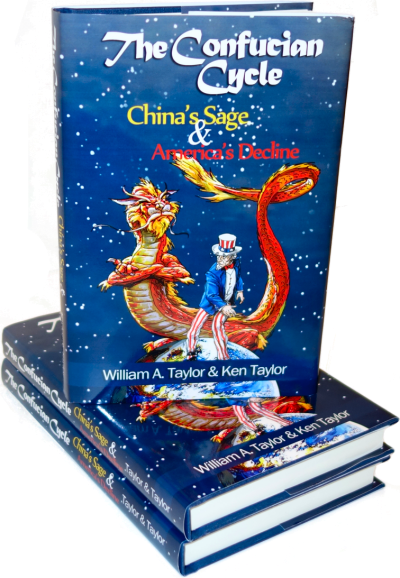
What does Chinese history have to teach America that Mr. Trump's cabinet doesn't know?

I missed President Trump's Jan 6 (?) speech live so I searched for it. I wanted to read it myself because there no sources reporting what he said. This was less than a week after his speech and it would not show up on google but it was the first result on duckduckgo. Hmmmmmmm
Even the geeks are catching on and viewing with alarm. "The Death of Freedom"
https://dzone.com/articles/the-death-of-freedom-by-software?edition=659391
on a software developer's discussion site points out that software developers aren't just observers, they're actively implementing censorship:
As software engineers and developers, we are not afforded the luxury of being simple observers; unlike speech suppression of the past, we are the ones on the frontlines. It is no longer some obscure aberration that censors speech from on high, but it is us creating these systems that are cracking down on offensive speech. We are no longer passive on-lookers, but rather, active participants.
The author explains the difference between cancel culture and the normal competition of ideas to which we've been accustomed:
This is not the case with suppression of speech. To suppress speech, we must assume our judgment of speech is inherently superior to another person's judgment. Thus, we baselessly claim we have the authority to determine which speech is permissible and which speech is not. No longer do we battle out ideas and concepts in the open, satisfied that our strongest beliefs will stand the test and our weakest beliefs will be shattered and replaced with ideas closer to the truth. Instead, we deem ourselves arbitrators of what others can or cannot say.
This superiority hinges on the belief that we hold some trait that another does not which provides us with this moral authority. It cannot be a trait common to all humans, lest our subjugated person lay the same claim against us and stifle our speech. Instead, it must be something only we possess.
Commercial competition involves making the world a better place by introducing new products and services. Cancel culture participants are convinced the will make the world a better place, but in a totally different way.
he danger in speech suppression is not that it is some cheap trick used by its practitioners here or there to gain a quick dollar, but instead, it is a moral imperative. Those who suppress speech do so because they believe they are doing the right thing. As observed by C.S. Lewis, this is the greatest of all tyrannies: That one person harms another thinking it is for the victim's own good. Unlike outright immorality (like robbery), this type of tyranny does not sleep because the perpetrator believes that he or she is making the world a better place.
Had these "moral busybodies" of today been an insignificant minority, there would be no need to write this article, but unfortunately, speech suppression is not a onesie-twosie occurrence. Instead, it has become a systemic, coordinated type of tyranny. And doubly-unfortunate, it is us - software engineers - who have become creators of this suppression machine. In the past, suppressing speech would require going door-to-door like Bradbury's fireman to find banned books, threatening publishers to cease printing of certain materials, or burning down a business to make a point. But in our modern age, suppression has become simultaneously more insidious and comprehensive.
It's not just geeks - some of the popular you Tube video starts are building their own sites "just in case."
https://www.bbc.com/news/technology-55349255
But Google-owned YouTube gets most episodes of Linus Tech Tips a week late.
Now, they debut on his own site called Floatplane, which attracts a much smaller crowd.
"Google has been very, very good to me," Linus says. "But it's a lot of eggs in one basket."
And with a staff of two dozen, he cannot rely on the company to continue being what he calls his "benevolent overlord".
He is not the only YouTube star looking for alternatives.
Another potential option of hiding oneself on the Internet would be to use a virtual machine for browsing......
@David - you are right, but that, too, is a lot of work. The Chinese count on most people not knowing how to do that.
MIT's technology review is totally on the side of Facebook censorship:
https://www.technologyreview.com/2021/03/11/1020600/facebook-responsible-ai-misinformation/
They say that the Cambridge Analytica "scandal," which benefitted Mr. Trump, was the first data breach in Facebook history. They ignore the fact that Facebook employees were embedded in Mr. Obama's 2 campaigns and had high-level access to Facebook data to help Mr. Obama influence voters.
This was OK, of course - Democrat privilege. They even boasted about it.
This is how they start:
It was March 23, 2018, just days after the revelation that Cambridge Analytica, a consultancy that worked on Donald Trump's 2016 presidential election campaign, had surreptitiously siphoned the personal data of tens of millions of Americans from their Facebook accounts in an attempt to influence how they voted. It was the biggest privacy breach in Facebook's history, ...
There's another advantage of Dissenter over either Chrome or Firefox - both those browsers do a lot of disk I/O even when you aren't looking at any new pages. That's a bummer - why should either browser be flailing your disk when you aren't looking at any new pages?
They also burn a lot of memory - you have to delete all stored disk data and cookies and shut the browser down every so often so they'll give back system memory. The ought to give back memory when you close a tab, but they don't.
Forbes has realized that Google Chrome really abuses user data. So much for "don't be evil":
https://www.forbes.com/sites/zakdoffman/2021/08/28/stop-using-google-chrome-on-windows-10-android-and-apple-iphones-ipads-and-macs/
Why You Should Delete Google Chrome After New Tracking Admission
A shocking new tracking admission from Google, one that hasn't yet made headlines, should be a serious warning to Chrome's 2.6 billion users. If you're one of them, this nasty new surprise should be a genuine reason to quit.
Behind the slick marketing and feature updates, the reality is that Chrome is in a mess when it comes to privacy and security. It has fallen behind rivals in protecting users from tracking and data harvesting, its plan to ditch nasty third-party cookies has been awkwardly postponed, and the replacement technology it said would prevent users being profiled and tracked turns out to have just made everything worse.
"Ubiquitous surveillance... harms individuals and society," Firefox developer Mozilla warns, and "Chrome is the only major browser that does not offer meaningful protection against cross-site tracking... and will continue to leave users unprotected."
Google readily (and ironically) admits that such ubiquitous web tracking is out of hand and has resulted in "an erosion of trust... [where] 72% of people feel that almost all of what they do online is being tracked by advertisers, technology firms or others, and 81% say the potential risks from data collection outweigh the benefits."
Amazon's crackdown on web sites that say things they dislike is getting worse:
https://thefederalist.com/2021/09/07/how-the-amazon-web-hosting-crackdown-threatens-patreon-substack-and-you/
How The Amazon Web Hosting Crackdown Threatens Patreon, Substack, And You
Last week, Reuters reported based on two anonymous sources that Amazon Web Services, which controls 40 percent of web hosting in the world, "plans to take a more proactive approach to determine what types of content violate its cloud service policies."
"Over the coming months, Amazon will hire a small group of people in its Amazon Web Services (AWS) division to develop expertise and work with outside researchers to monitor for future threats, one of the sources familiar with the matter said. It could turn Amazon, the leading cloud service provider worldwide with 40% market share according to research firm Gartner, into one of the world's most powerful arbiters of content allowed on the internet, experts say."
Amazon declined to comment to Reuters for the story, then after the article published sent a statement insisting the report was "wrong," claiming, "'AWS Trust & Safety has no plans to change its policies or processes, and the team has always existed.'"
"We've always reserved the right to police who is allowed to speak on our internet" is not a very comforting response to an article alleging a coming content crackdown. In addition, to this post-publication claim from Amazon, "A Reuters spokesperson said the news agency stands by its reporting."
Don't forget the context: The Biden administration revealed a few weeks ago that they, mafia-like, pressure big tech entities like Facebook and Twitter to remove information that contradicts their political goals. ("That's an, um, 'misinformed' piece of content over there on your platform. Sure would be a shame if the super-touchy Democrats controlling the entire federal government decided it was a reason to regulate and legally harass you.")
The reported Amazon Web Services crackdown also comes in the wake of news that the Jan. 6 congressional committee subpoenaed the cell phone records of GOP lawmakers, including the House minority leader, from their service providers, which already help the federal government spy on Americans through routinely recording the contents of everyone's texts and calls.
And it gets worse from there.